The news related to Zoom has been astounding in recent weeks. No doubt you’ve heard about the meetings hijacked by some loon who goes on to share pornographic images or videos. There are also issues with some groups getting invites for sessions they aren’t supposed to attend. All of this while they struggle to keep up with demand.
Webex has been caught up in a phishing scam, and GoToMeeting has had its struggles.
What we should take away from this is the importance of conferencing security. While we want to talk about 1080p webcams and if emojis are available for chats, it’s just as important to discuss security needs.
In the rest of the blog, we’ll evaluate the security related to our solutions.
Web Conferencing Security
At MeetingOne, we have long prioritized security. We’ve factored it into the products we develop, the carriers we use, and who our partners are.
Let’s start with our most important partner: Adobe Connect.
Adobe Connect: FedRAMP Compliant
Adobe Connect is the premier web conferencing platform on the market. It’s known for the ease with which rooms can be customized; the persistence of rooms and content after a room is closed; the immersive experience individuals enjoy when they participate in Connect.
While all these factors are fantastic, Adobe is also committed to security. Heck, security might be one of its strongest points.

First and foremost, Adobe Connect is FedRAMP compliant. Here’s a quick run-down on what you need to know about FedRAMP:
- FedRAMP standards are following legislation outlined by FISMA, and they meet the baseline security controls set out by NIST in their special publication 800-53.
- As defined by the NIST, security controls are the safeguards and countermeasures used by a particular information system to protect confidential and integral parts of that system.
- In all, there are 18 “families” of security controls that range from system configuration management to physical and environmental protection. Within each family, there are numerous sub-categories with hundreds of specific security controls.
- If your web conferencing platform is FedRAMP compliant, it will hold the “Agency FedRAMP Authorization” title.
Being FedRAMP compliant makes Adobe Connect one of the few platforms available to government agencies with the highest conferencing security needs.
Adobe just put out a blog talking to the strengths of Adobe Connect security. Here were some of the most interesting excerpts regarding their approach to security:
-
Secure Code Design
Through the Adobe Secure Product Lifecycle (SPLC), we start with a set of development guidelines that our programmers use when writing our code, keeping security as a high priority.
-
Secured Connection
Next, our servers, and how we communicate over the internet, use industry-standard encryption practices – communicating over HTTPS employing Transport Layer Security (TLS) cipher suite to help secure your data in transit using AES-256. We add additional encryption for the most critical data, using SHA-256 hashing for passwords.
-
Least privilege principle as a default
Administrators can enforce appropriate restrictions for all users. Using our years of product design experience aligned to the toughest customer use cases in most regulated industries, we have created user interfaces and configuration settings that follow a ‘Least Privilege Principle.’ This essentially means that as a default meeting host has the greatest control, and others join with the least level of privilege. Meeting hosts control not only who can enter a meeting but also the assignment of role-based privileges to co-presenters and participants.
Each organization has its own set of unique requirements – we offer the flexibility to tailor each account to match those needs. Account Administrators can choose secure two-factor authentication and Single Sign-On (SSO) for IT-controlled logins. Applications can be whitelisted for approved application sharing or blacklisted to be always be hidden. Meetings can be permanently blocked against ‘guest’ access so that only employees and pre-registered users attend.
-
Deployment flexibility with Managed Services
Our customers can choose from a variety of deployment options ranging from a hosted service on Adobe managed infrastructure leveraging industry best practices for secure design. Or a private cloud deployment by certified cloud infrastructure providers to operate and manage their services. Or even an on-premise deployment behind an organization’s firewall.
Perhaps, one of the reasons for being the trusted solution of choice for the most’ locked down’ regulated environments is the gamut of validations from industry compliance and regulatory bodies. Depending on the deployment model, Connect meets various regulated industry security standards and has received many certifications attesting to its security. This makes it suitable for specific industries’ needs. These cover financial institutions by being GLBA-ready, US federal government with FedRAMP certification, healthcare and non-profit organizations by being HIPAA-ready, and universities and K12 institutions, by being FERPA-ready.
Adobe’s attention to security has made Connect a great platform for most agencies around the country – and the world – to use!
Get more ideas for what makes a web conferencing platform secure here.
Audio Conferencing Security
The MeetingOne Bridges
Our bridge has evolved over the years to meet conferencing security needs. Earlier iterations covered intrusion and fraud detection. Encrypting communications has also been addressed. All communication over our bridge is encrypted with AES-256 bit, and we utilize SSL.
After calls, we layer symmetric & asymmetric encryption to protect the keys used to get recordings. The “computational complexity” of this approach ensures recordings are always secure.
Click&Meet and Online Account Management
We also put conferencing security controls in the hands of our users. With Click&Meet and OAM, people are ready every day to host secure calls – or use our audio integration to support Connect events, trainings, and meetings.
Let’s look at a few examples where these tools help.
Parameters
Establishing conferencing parameters, such as maximum numbers of participants, sub-conference rooms, and inactive time, help you keep track of participant movement.
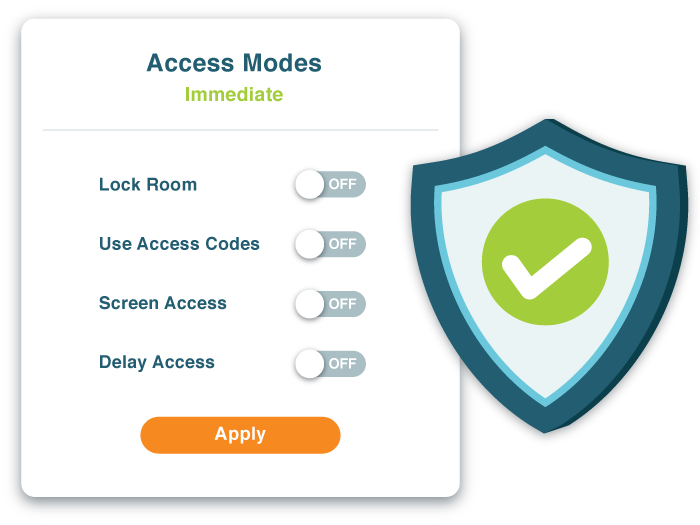
Access Modes
Click&Meet provides hosts four easy ways to define access:
- Delayed: Hosts set the amount of time they want before someone can leave the “Waiting Lounge” and join the main conference. This gives hosts a chance to observe who joins the call.
- Screened: Participants can’t enter until the host has vetted them. Click&Meet offers a Host Corner where these conversations can happen.
- Coded: There’s an unfortunate but very real fact: Anyone can get a conference phone number. That individual can then sneak into your conference calls. To prevent these potential break-ins, we provide several different Code options.
- First of all, every host gets a PIN. This prevents someone from using your line without you knowing. Also, hosts can use two different code types to define access to the room, Room Access Codes (RACs) or Individual Access Codes (IACs).
- RACs are pretty standard in the conferencing world. A RAC is a common number every enters to join a call. Set to RAC, and only people with the code can join.
- Unique to MeetingOne, IACs codes are like fingerprints. Each one assigned is unique to that person. Setting a room to IACs means only people who have them can join. Very powerful, indeed! If you don’t have the code, you don’t get in.
- RACs and IACs can be layered, too, for double the security.
- Locked: The Fort Knox of access modes, locking your room prevents anyone from joining. Hosts often use this access mode once their call has started, ensuring no one else joins later. With Click&Meet, you can lock your room from the outset then dial-out to the people you want on your call.
Whatever mode you choose, there’s no denying the power of access modes.
Providing conference codes is likely the most crucial step in preparing the security of an audio conference. Using codes helps limit two potential threats: outside conference hackers, and unwanted internal leaks.
In-Call Features
Security isn’t limited to event prep. In-call features are important, too. Here are some we like to highlight:
- Interface: Click&Meet is a slick interface that allows hosts to perform all the actions of a standard conference call from their computer! Using this interface, it’s easy for hosts to:
- Mute one or all callers
- Disconnect one caller
- Rename caller avatars
- Add callers to the built-in directory.
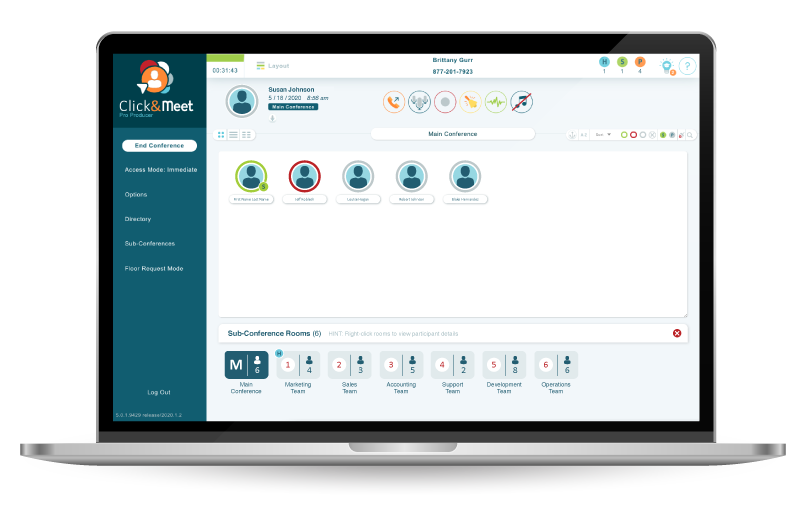
- Dial-out: Mentioned in conjunction with Locked Access, dialing out ensures only the people a host wants on their calls are part of the conversation. Click&Meet has a directory feature you can use to add all your contacts. It’s as easy as selecting all the callers you want to start the call.
- Roll-Call: Pretty standard. Set up roll call to know who joins your call.
Get more ideas for what makes an audio conferencing platform secure here.
Through and through, our conferencing solutions are geared toward the highest security needs!
Pairing Adobe Connect & MeetingOne ensures you can meet or train safely.
Meet, Train, Present – Securely
Zoom is in a catch-22. They wanted their platform to be easy to use and accessible. These factors make their platform vulnerable. To address security, they will likely have to make their platform harder to use and access.
Some credit is due. Their 90-day security plan is good. But I worry about their broader perspective on security.
In July of 2019, Zoom was notified they had a security hole that made it easy for hackers to join random Zoom meetings! IN 2019!!!
They said they patched this problem, but here we are, discussing Zoom-bombing and their security vulnerabilities. These are indications about the value they place on a secure platform.
Zoom isn’t going to cut it for organizations with pressing security needs. Could you imagine the DoD getting Zoom-bombed? It won’t happen because they rely on Adobe Connect and MeetingOne audio.
We’re proud to stand behind our commitment to conferencing security. If you’d like more information about our commitment to conferencing security, check out this page.
Otherwise, I’d invite you to start a conversation with our team.